Decoding Kubernetes Ingress auth Secrets
Update: In the comments, the following one-liner is suggested by Matt T if you have
jqinstalled (a handy utility if there ever was one!):
kubectl get secret my-secret -o json | jq '.data | map_values(@base64d)'
I figured it would be handy to have a quick reference for this, since I'll probably forget certain secrets many, many times in the future (I'm like that, I guess):
I have a Kubernetes Secret used for Traefik ingress basic HTTP authentication (using annotation ingress.kubernetes.io/auth-secret), and as an admin with kubectl access, I want to see (or potentially modify) its structure.
Let's say the Secret is in namespace testing, and is named test-credentials. To get the value of the basic auth credentials I do:
kubectl get secret test-credentials -n testing -o yaml
This spits out the Kubernetes object definition, including a field like:
data:
auth: [redacted base64-encoded string]
So then I copy out that string and decode it:
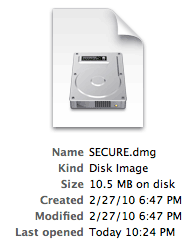 The popularity of 'cloud file management' software such as Dropbox and SugarSync has made me re-evaluate my security practices for files on my computers; in the past, I have not put any of my private files (for instance, files with sensitive passwords, or scans of important legal documents) on my shared folders (Dropbox, iDisk, etc.), but I finally came up with an ideal solution to storing and syncing these files. It's like using FileVault, but without the extra overhead of securing every file in your home directory.
The popularity of 'cloud file management' software such as Dropbox and SugarSync has made me re-evaluate my security practices for files on my computers; in the past, I have not put any of my private files (for instance, files with sensitive passwords, or scans of important legal documents) on my shared folders (Dropbox, iDisk, etc.), but I finally came up with an ideal solution to storing and syncing these files. It's like using FileVault, but without the extra overhead of securing every file in your home directory.