I've helped many people set up or fix a botched install of Apache Solr on their VPSes and web servers. Most of the time, I've noticed that people leave the administrative frontend to Solr wide open for anybody on the internet to access, by just accessing http://example.com:8983/solr. This is very dangerous, as not only can anyone browse and query your search indexes, they can even add, delete, or change your search cores, and see sensitive system information that can be used to gain further access!
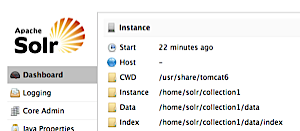
The Apache Solr admin dashboard
There are a few different ways you can lock down access to a solr server, and besides setting up basic HTTP authentication in Tomcat for Solr access, the simplest way is to limit access to port 8983 to either localhost (if solr/tomcat is running on the same server as your website that's using solr), or a specific IP address (if solr/tomcat is on a separate server), using iptables.
The two commands to configure this are:
sudo iptables -A INPUT -p tcp -s localhost --dport 8983 -j ACCEPT
sudo iptables -A INPUT -p tcp --dport 8983 -j DROPThe first command tells iptables, "accept all connections from localhost on port 8983", and the second tells iptables, "drop all traffic to port 8983"—since iptables obeys rules in order from top to bottom, localhost traffic is let through, while other traffic is denied.
To save these rules permanently (so they'll persist after a reboot) on CentOS 6.x, make sure you save the firewall configuration with sudo service iptables save
If you ever need to access the administrative Solr dashboard again, you could insert another rule earlier in the iptables rule chain allowing access to port 8983 to your computer's IP address, then delete that rule when you're finished working on the dashboard.
Note: If you're using Jetty instead of Tomcat, just substitute port 8080 for 8983 in all the above directions.
Comments
thanks a lot..
you can use -Djetty.host=0.0.0.0
thanks. it was very helpful
You should use
-i loinstead of-s localhost. This will restrict it to traffic on the loopback adapter instead of checking traffic on any adapter for a specific IP address. Only localhost traffic can occur on the lo adapter.One way protect port 8983 while retaining access is to set up a SSH tunnel. First, follow Jeff's instructions for using the two iptables commands and saving them permanently. Then create a saved session in PuTTY with the Host Name for the Solr server. Go to Connection > SSH > Tunnels, set Source port = 8983 and Destination = localhost:8983, and Add this is a forwarded port. Now, save the session with whatever name you choose. While you are logged onto the server via this saved session, you can access the Solr admin panel in your browser on the same computer via localhost:8983/solr.
How can I restrict access to port 8983 from outside on a windows server?
It looks like this tutorial on managing the Windows Server firewall might be of help.
Thank you !
Thank you!